Posted in 2021
Asleep at the Keyboard? Assessing the Security of GitHub Copilot’s Code Contributions
- 29 December 2021
- Deep Learning
Paper: https://arxiv.org/pdf/2108.09293.pdf
Codex: https://arxiv.org/pdf/2107.03374.pdf
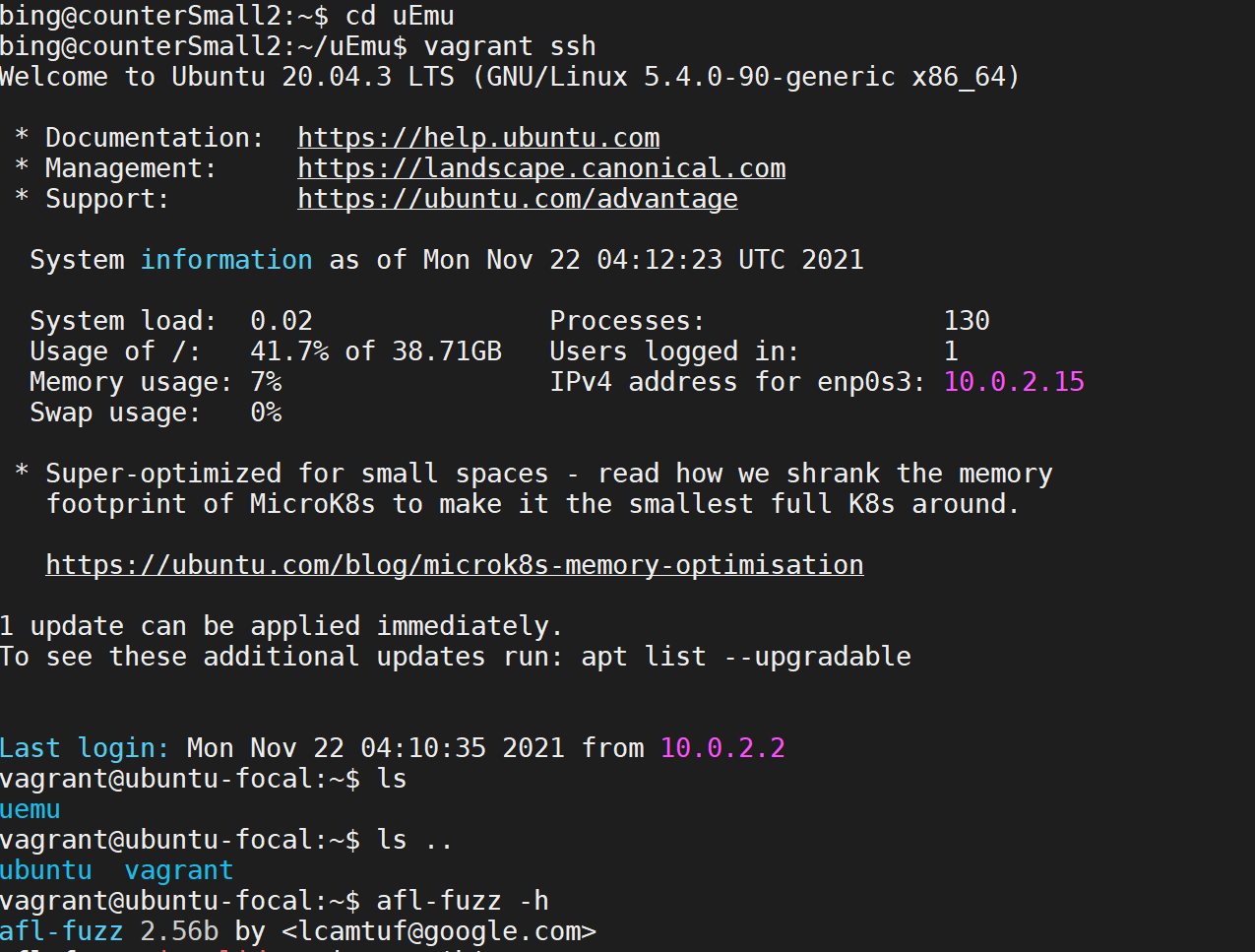
Automatic Firmware Emulation through Invalidity-guided Knowledge Inference
- 17 November 2021
- Firmware
Link: https://www.usenix.org/confere/usenixsecurity21/presentation/zhou
Code: https://github.com/MCUSec/uEmu
A Survey on Security of Automatic Generated Code
- 10 November 2021
- Software Engineering
Towards Automatic Generation of Vulnerability-Based Signatures
Exploiting and Protecting Dynamic Code Generation (NDSS’ 15)
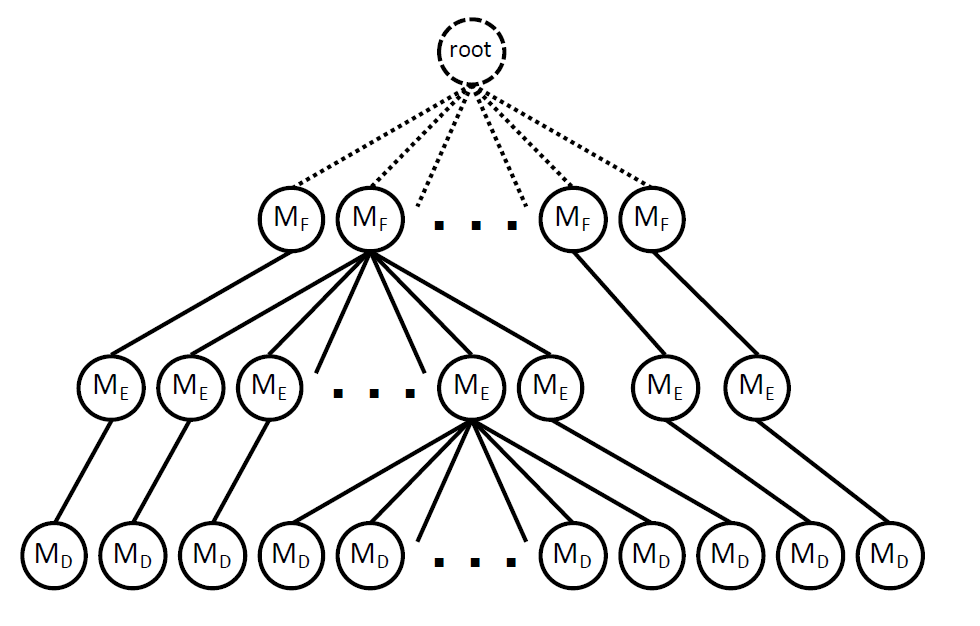
Reinforcement Learning-based Hierarchical Seed Scheduling for Greybox Fuzzing
- 04 November 2021
- Software Engineering
paper link: https://www.cs.ucr.edu/~heng/pubs/afl-hier.pdf
video: https://www.youtube.com/watch?v=E90gL7q-IVQ
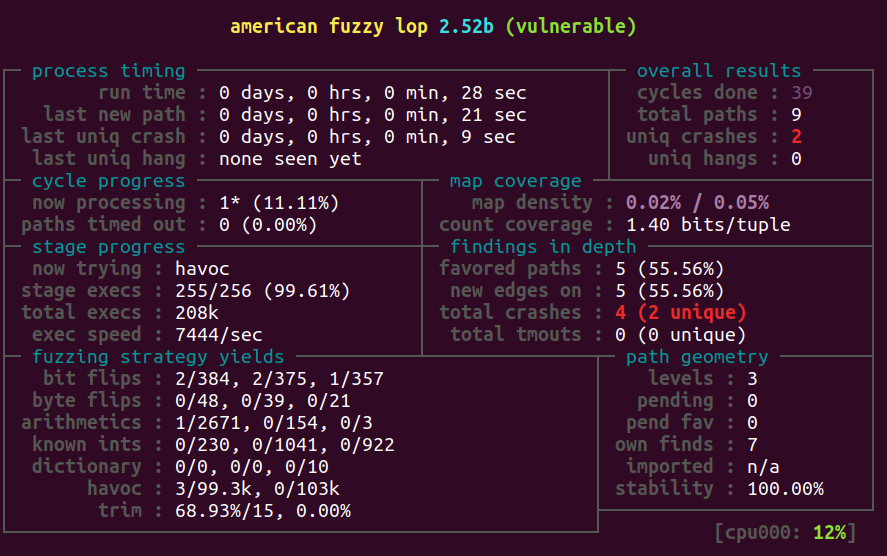
A Survey on Fuzzing
- 27 October 2021
- Software Engineering
Conceptually, a fuzzing test starts with generating massive normal and abnormal inputs to target applications, and try to detect exceptions by feeding the generated inputs to the target applications and monitoring the execution states. 1
Fuzzing with AFL workshop: AFL training
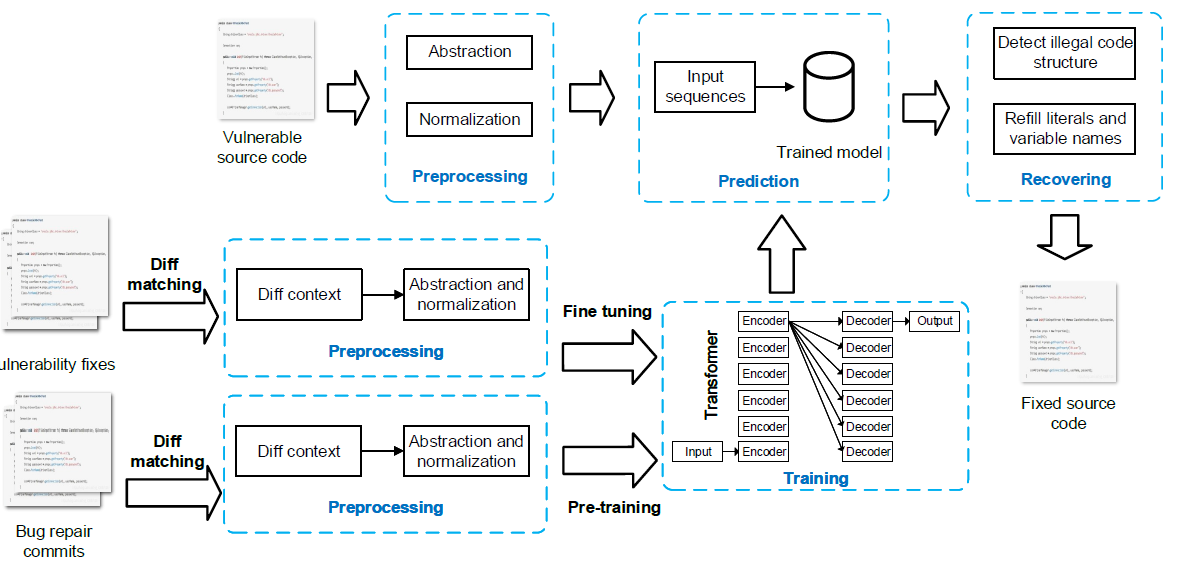
SeqTrans: Automatic Vulnerability Fix via Sequence to Sequence Learning
- 20 October 2021
- Software Engineering
Link: https://arxiv.org/pdf/2010.10805
Software vulnerability can be viewed as a specific category of bugs that are still mainly solved by programmers’ manual efforts. An automated method based on Neural Machine Translation (NMT), which is previously used for bugs repairs, can also be transfered to target on the vulnerability fixes after fine-tuning.
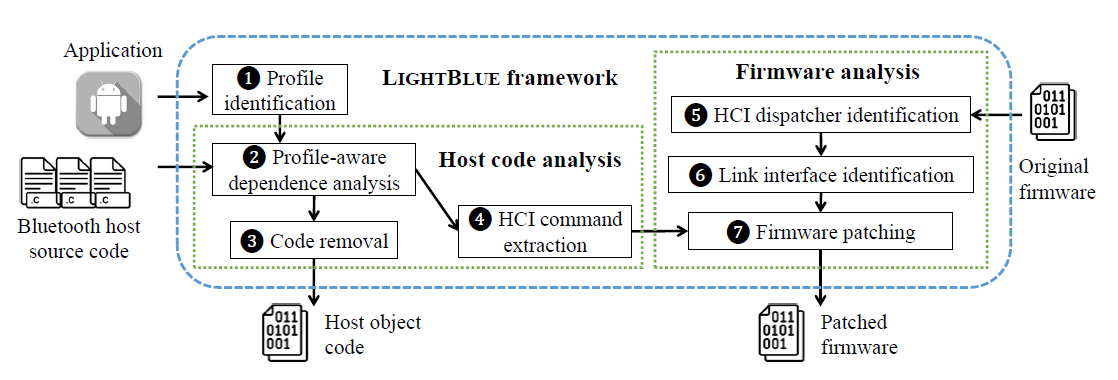
LIGHTBLUE: Automatic Profile-Aware Debloating of Bluetooth Stacks (USENIX Security’21)
- 25 September 2021
- Firmware
Paper & Presentation: https://www.usenix.org/conference/usenixsecurity21/presentation/wu-jianliang
Bluetooth standards and their implementations are diverse and complex, which contains many functionalities that never be required in the common scenarios. Those useless parts actually extend the attack surface.